Over the past decade, innovation has played an increasingly significant role in the health industry. The med-tech sector has witnessed notable trends such as integrated solutions, regulatory advancements, smarter devices, and real-time analytics, as highlighted in a recent McKinsey report.
New software solutions have contributed to improved medical treatments, addressed various healthcare challenges, and elevated the overall performance of the industry. However, these advancements have also brought about concerns regarding data security in healthcare. Let's explore further details about data security in healthcare software via this article!
>> Read more:
Increased Demand for Data Security in Healthcare Sector
The protection of sensitive information, known as Protected Health Information (PHI), has become a critical issue. Reports from the Health Insurance Portability and Accountability Act (HIPAA) Journal indicate that in 2020 alone, during the onset of the pandemic, over 30 million medical records were compromised.
The health industry experiences more data breaches than any other sector, making it vulnerable to cyber threats. Stolen patient records are highly valuable on the black market, with each record fetching up to $363.
Criminals can exploit this information for fraudulent activities, scams, or even blackmailing individuals based on their physical or mental health conditions. Consequently, these data breaches raise significant concerns among governments, healthcare providers, and patients about information security in the healthcare domain.
In light of these challenges, this article aims to emphasize the critical importance of data security in healthcare applications. It will outline the general requirements for ensuring data security in healthcare applications and offer insights into effective measures to meet these requirements.
Safeguarding patient data is of paramount importance to protect both individuals and the integrity of the healthcare industry as a whole.
The Significance of Data Security in Healthcare Systems
When developing healthcare systems, it is crucial to protect sensitive information, collectively known as Protected Health Information (PHI). PHI encompasses various patient details, including legal names, home addresses, social security numbers, demographics, medical histories, insurance coverage, lab test results, and more.
Exposure of PHI, often caused by inadequate data security measures within the organization, can have severe consequences for both the healthcare provider and the patient. The repercussions may include penalties, costly lawsuits, and compensation fees, resulting in significant financial losses and damage to the provider's reputation.
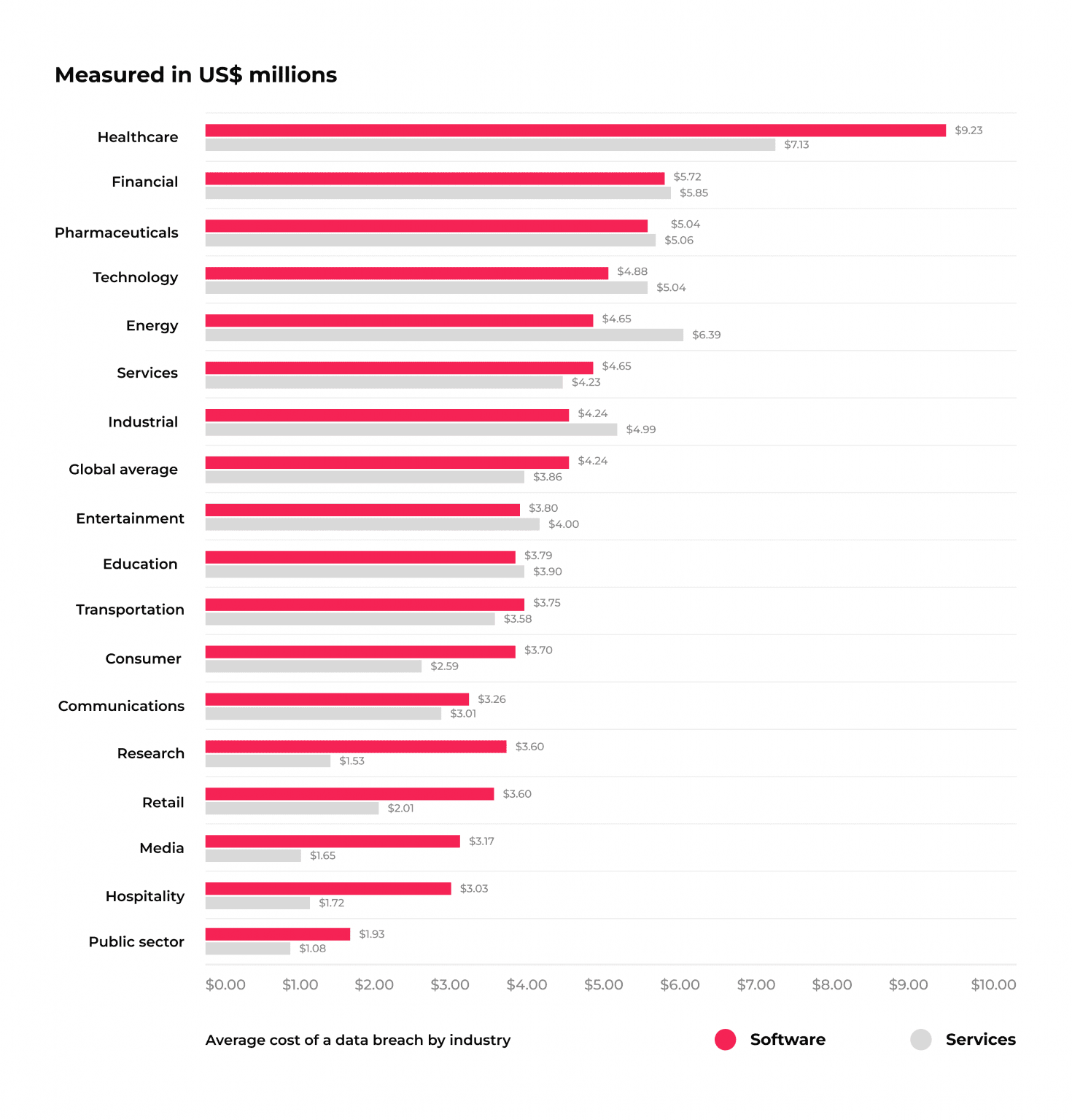
In 2021, the total cost of data breaches in the medical information services industry exceeded $9 million.
For patients, stolen PHI can lead to identity theft and potential blackmail attempts to regain control of their information. Moreover, this unauthorized access to patient data poses a direct threat to their health as it hinders their ability to access critical medical histories and treatment reports.
Given these potential risks, ensuring robust data security measures in healthcare systems is of utmost importance to safeguard patient information, protect healthcare providers from legal and financial implications, and maintain the trust of patients in the healthcare industry.
Understanding Healthcare Data Security Fundamentals
Protected Health Information (PHI) encompasses various sensitive data related to patients, such as identity, medical history, laboratory results, insurance coverage, and other information linked to specific individuals. The disclosure of PHI can lead to harm for the affected individuals and result in penalties for institutions or businesses that fail to uphold data privacy standards in healthcare.
Not all healthcare apps are subject to the same healthcare data protection regulations across different countries. The need to comply with these regulations can be determined by assessing the functions and features of the app in question.
Fitness applications, healthcare education platforms, medical reference tools, fitness or yoga apps, and treatment reminders not involve entering, processing, or exchanging highly specific user data typically do not require strict regulatory compliance.
However, regional and international regulations must be followed if the app falls under the category of:
- Healthcare reference and database apps;
- Professional networking apps;
- Custom doctor appointment and clinical assistance apps;
- Patient tracking apps;
- Custom telehealth mobile apps (doctor-on-demand apps).
These types of applications deal with personal healthcare information that needs to be securely stored, transmitted, and analyzed by various institutions, necessitating strong protection against third-party intervention.
Ensuring compliance with relevant healthcare data protection regulations is essential to maintain the privacy and security of patient information and to foster trust between users and healthcare institutions or providers.
>> Read more:
- 15 Essential Tips for Enhancing Healthcare UI Design in Mobile Apps
- 8 Main Benefits of Healthcare Automation Systems
Healthcare Data Protection in Different Countries
Healthcare data information protection is a global concern, and different countries have established their own regulations and laws to ensure the privacy and security of patient information. Below are some examples of how healthcare data information protection is addressed in different countries:
HIPAA Regulations in the U.S.
The Health Insurance Portability and Accountability Act (HIPAA) is a comprehensive set of regulations enacted in the United States in 1996. HIPAA's primary focus is to protect the privacy and security of individuals' health information, known as Protected Health Information (PHI). The regulations apply to covered entities and business associates that handle PHI in the healthcare industry.
Key components of HIPAA regulations include:
Privacy Rule: The HIPAA Privacy Rule establishes national standards to protect individuals' medical records and other personal health information. It governs how healthcare providers, health plans, and healthcare clearinghouses handle PHI and ensures patients have control over their health information.
Covered entities must obtain patient consent for the use and disclosure of PHI, except in cases related to treatment, payment, or healthcare operations.
Patients have the right to access their own health information and request corrections if necessary.
Covered entities are required to appoint a Privacy Officer to oversee compliance with the Privacy Rule.
Security Rule: The HIPAA Security Rule sets standards for the protection of electronic PHI (ePHI) that is created, received, used, or maintained by covered entities and business associates.
Covered entities must implement administrative, physical, and technical safeguards to protect ePHI from unauthorized access, disclosure, and alteration.
Risk assessments and regular audits are required to identify vulnerabilities and address security risks.
Breach Notification Rule: The HIPAA Breach Notification Rule mandates covered entities to notify affected individuals, the Department of Health and Human Services (HHS), and the media (in certain cases) in the event of a breach of unsecured PHI.
Enforcement: The Office for Civil Rights (OCR), a part of the HHS, is responsible for enforcing HIPAA regulations. Non-compliance with HIPAA can result in substantial fines and penalties.
PIPEDA Regulations in Canada:
In Canada, healthcare data protection is governed by the Personal Information Protection and Electronic Documents Act (PIPEDA) and provincial health privacy legislation in some provinces. PIPEDA sets out guidelines for the collection, use, and disclosure of personal information, including health-related information, by private-sector organizations.
Key aspects of PIPEDA in relation to healthcare data include:
- Consent: Organizations must obtain meaningful consent from individuals before collecting, using, or disclosing their personal information, including health information.
- Limiting Collection and Use: Organizations must limit the collection and use of personal information to purposes that a reasonable person would consider appropriate under the circumstances.
- Security Safeguards: Organizations are required to implement security safeguards to protect personal information against loss, theft, unauthorized access, and disclosure.
- Accountability: Organizations are accountable for the personal information they hold and must designate individuals responsible for ensuring compliance with PIPEDA.
- Access and Correction: Individuals have the right to access their personal information held by an organization and to request corrections if it is inaccurate or incomplete.
- Breach Notification: PIPEDA does not explicitly require mandatory breach notification like HIPAA. However, organizations are encouraged to notify affected individuals and the Office of the Privacy Commissioner of Canada (OPC) in the event of a data breach.
GDPR Regulations in Europe
When targeting the international market, compliance with the General Data Protection Regulation (GDPR) is crucial, especially for businesses operating in the United Kingdom and European Union. Adopted in 2018, GDPR regulates the exchange of data between EU member states and aims to safeguard the electronic personal healthcare information of EU residents.
Furthermore, some non-EU countries, including Serbia, Norway, and Iceland, have either accepted GDPR or adapted similar regulations for their healthcare sectors.
The GDPR system encompasses a wide range of software and has more generalized regulations compared to the Health Insurance Portability and Accountability Act (HIPAA). To gain approval for a healthcare app in Europe, it is imperative to adhere to these regulations:
- Consent and Data Processing: Obtain explicit and informed consent from users before processing their personal healthcare data. Users must be informed of the purpose, scope, and duration of data processing.
- Data Minimization: Only collect and process the minimum necessary personal healthcare data required for the app's intended functionality. Avoid excessive data collection.
- Purpose Limitation: Use personal healthcare data only for the specific purposes for which users have provided consent. Avoid using data for unrelated or incompatible purposes.
- Data Accuracy: Ensure that personal healthcare data is accurate and up-to-date. Provide mechanisms for users to update their information.
- Data Security: Implement robust data security measures to protect personal healthcare data from unauthorized access, loss, or disclosure. Encryption, access controls, and secure storage are essential.
- Data Retention: Set specific retention periods for personal healthcare data and delete or anonymize it once the purpose for which it was collected is fulfilled.
- Data Subject Rights: Respect users' rights under GDPR, including the right to access, rectify, erase, and restrict the processing of their personal healthcare data.
- Data Transfers: If transferring personal healthcare data outside the EU, ensure that appropriate safeguards are in place, such as Standard Contractual Clauses or Binding Corporate Rules.
- Data Protection Officer (DPO): Appoint a Data Protection Officer responsible for overseeing data protection compliance within the organization.
- Privacy Policy: Provide a clear and comprehensive privacy policy that outlines how personal healthcare data is handled, the purposes of processing, and users' rights.
International Standards in the Asia-Pacific Region
In the Asia-Pacific region, medical information is governed by various laws that bear similarities to the General Data Protection Regulation (GDPR) while accounting for each region's specific regulatory requirements, enforcement mechanisms, and data export regulations.
Here is a list of countries in the Asia-Pacific region and their respective personal health data rules, ranked by the level of regulation, starting from the highest:
- China - Cybersecurity Law
- South Korea - Personal Information Protection Act
- Taiwan - Personal Data Protection Act
- India - Digital Information Security in Healthcare Act
- Australia - Privacy Act
Complying with regulations like HIPAA in the US, PIPEDA in Canada, GDPR in the EU, and other relevant laws is crucial before launching healthcare data security software in these regions. Additionally, continuous improvement of the app is essential to proactively prevent third-party intervention and maintain data security standards.

Major Data Security Risks in Healthcare Systems
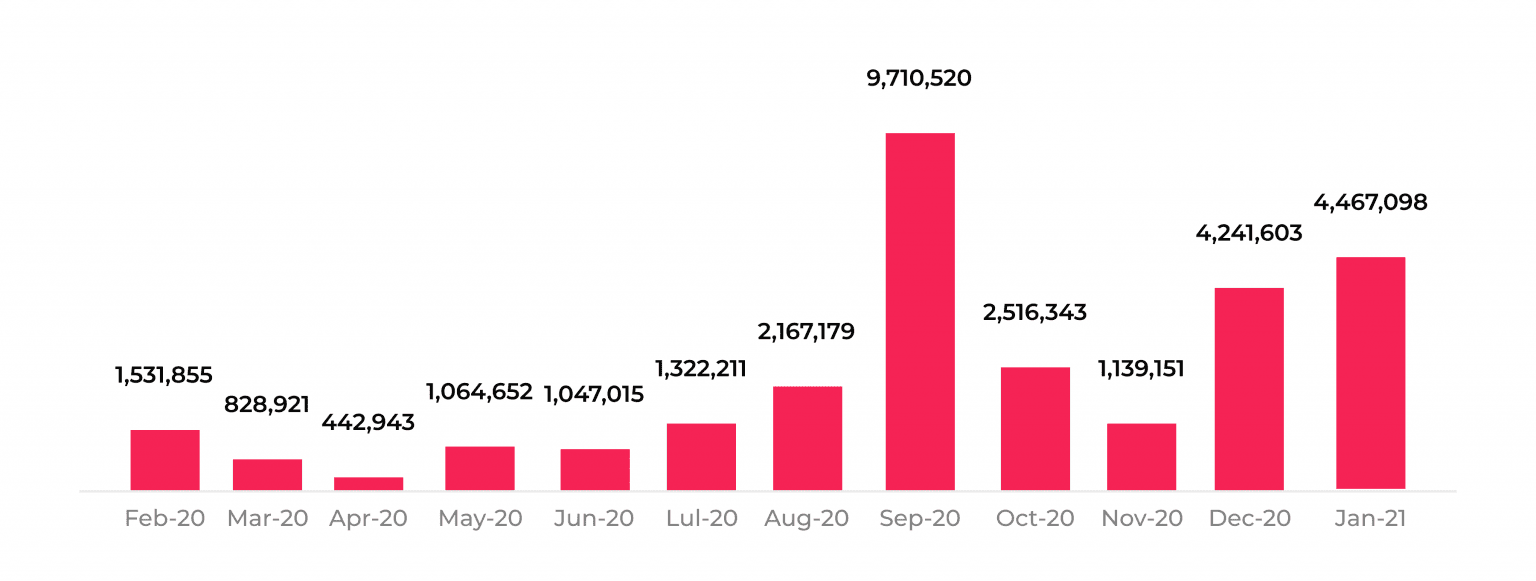
The alarming figures from the HIPAA Journal reveal that in January 2021 alone, 4,467,098 healthcare records were reported as breached. This number exceeded the total breaches in December 2020 by over 225,000 records and was four times higher than November's count. The magnitude of these breaches is even more shocking when considering that January witnessed fewer attacks than the preceding month.
As these attacks continue to escalate, they pose a significant threat and can lead to substantial losses for healthcare companies.
Understanding the weakest points that hackers target is crucial in preventing data breaches. Here is a concise list of critical factors to consider:
Challenges with Electronic Health Records (EHRs)
The adoption of Electronic Health Records (EHRs) has undoubtedly improved the customer experience in the healthcare industry, facilitating easy and quick access to patients' records by both doctors and patients across various devices. Health Information Exchanges (HIEs) have further streamlined processes, enabling productive collaboration between different departments and organizations.
However, the digital storage of sensitive patient information also introduces risks of exposure. The number of compromised EHRs has doubled between 2019 and 2021. Cybercriminals exploit various avenues, such as phishing, data breaches, or weaknesses in third-party systems during HIE, to gain unauthorized access to patient records.
Use of Outdated Software, Legacy Systems, and Obsolete Technologies
The adoption of EHRs has indeed improved healthcare institutions' performance, but it has also amplified the risk of cyberattacks. The use of outdated software, legacy systems, and obsolete technologies makes it easier for criminals to steal patients' data.
Transfer of Electronic Health Records
During EHR transfers, the stored data becomes more vulnerable to hacker attacks. The information can be easily copied by third parties, and system fragility during the transferring process may lead to data loss.
Third-Party Data Access
Third-party data access poses another significant risk that can severely impact a company's reputation and workflow. Hackers can exploit this vulnerability to disclose or sell clients' data.
User Errors & Insider Threats in Data Security
Insider threats refer to security risks posed by individuals who work or have worked within an organization. Shockingly, any employee typically has access to approximately 20% of sensitive files within the facility, making data breaches caused by doctors, medical staff, or current/former employees a significant concern.
For instance, simple actions like sending a patient's medical record details via email or text can create substantial security vulnerabilities. Additionally, storing sensitive data on personal devices and sharing it while using public Wi-Fi significantly increases the likelihood of cybercriminals gaining unauthorized access to the information.
Furthermore, the lack of regular employee and patient training on handling sensitive information further exacerbates the risk of data breaches. Proper education and training are crucial in cultivating a security-conscious culture that minimizes the chances of inadvertent mistakes leading to data exposure.
To mitigate these risks, organizations must implement strict access controls, enforce data security policies, and conduct regular training to educate employees and healthcare professionals on the importance of safeguarding sensitive information.
The Rise of Telehealth & Mobile Healthcare Apps
The global pandemic has accelerated the adoption of mobile telemedicine applications, allowing individuals to access medical services conveniently through their smartphones and tablets without the need to visit a physical hospital. While telehealth solutions offer enhanced accessibility for patients, they also bring forth new security challenges.
One significant concern is that patients may not always treat the information they share as sensitive and might overlook essential security measures, such as activating multi-factor authentication or setting strong passwords. Additionally, using mobile apps on devices connected to unprotected networks exposes them to potential data breaches, providing cybercriminals with numerous opportunities to exploit vulnerabilities.
Furthermore, wellness app development may not require the same level of compliance with industry user privacy standards as other healthcare software. This discrepancy poses another security threat, especially when users share personal information, including payment details, on these platforms.
To address these security risks, telehealth and mobile healthcare app developers must prioritize robust data encryption, user education on security best practices, and strict adherence to industry privacy standards. Proactive measures will ensure that these innovative healthcare solutions remain secure and safeguard patients' sensitive information effectively.
>> Read more:
- 5 Best Practices for Enhancing CI/CD Pipeline Security
- DevSecOps: Integrating Security into DevOps for Enhanced Software Development
Cloud and IoT Security Vulnerabilities in Healthcare
The widespread adoption of the Internet of Things (IoT) and cloud computing has become a common practice among healthcare organizations due to the efficiency gains they offer. However, as these technologies continue to evolve, many solutions lack robust built-in security measures, leaving critical data vulnerable to breaches.
Alarming statistics reveal that over half of healthcare organizations have recently experienced security incidents related to IoT and cloud systems. The data transmitted between devices and servers may be inadequately encrypted during transit, making the system susceptible to third-party intrusions.
Moreover, inadequate cloud computing configuration exacerbates security risks, creating an ambiguous direction for data security in the cloud and IoT domain. As healthcare organizations rely more on these technologies to streamline operations, it becomes imperative to implement stringent security protocols, including encryption, access controls, and continuous monitoring to safeguard patient data effectively.
Taking proactive steps to address these vulnerabilities will enhance data protection and foster greater trust in the use of cloud and IoT technologies in the healthcare industry.
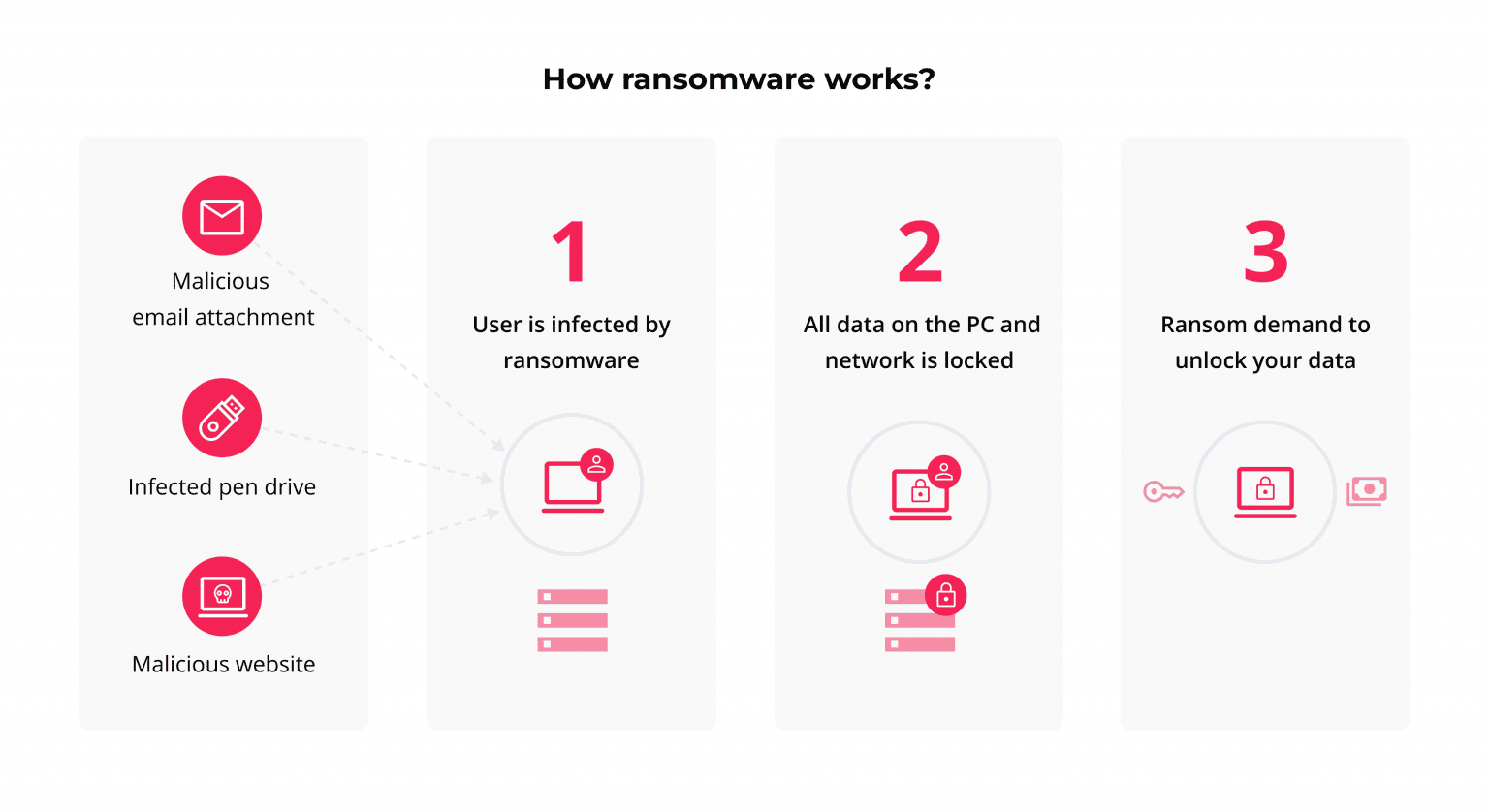
Ransomware Attacks
Ransomware attacks pose a significant threat in which individuals or organizations are denied access to their files, and the only means to regain control is by paying the cyber attackers. Phishing attempts and software or VPN configuration vulnerabilities are the most prevalent methods used to steal encryption keys and execute ransomware attacks.
While the primary motive behind ransomware attacks used to be data recovery upon payment, attackers have now escalated their tactics. They threaten to expose sensitive patient data unless the ransom demands are met, putting both the organization's reputation and the patient's identity at serious risk.
Best Solutions for Ensuring Data Security in Healthcare Apps
To enhance data security in your healthcare organization, consider implementing the following measures:
Regulation Compliance
Adhering to user privacy standards and regulations is crucial for safeguarding patient data. The most well-known regulations in the healthcare sector are HIPAA (Health Insurance Portability and Accountability Act) in the US and GDPR (General Data Protection Regulation) in the EU.
Regardless of your organization's location, compliance with these industry standards is essential to avoid data security risks, reputational damage, and penalties.
Data Access Control Through User Authentication
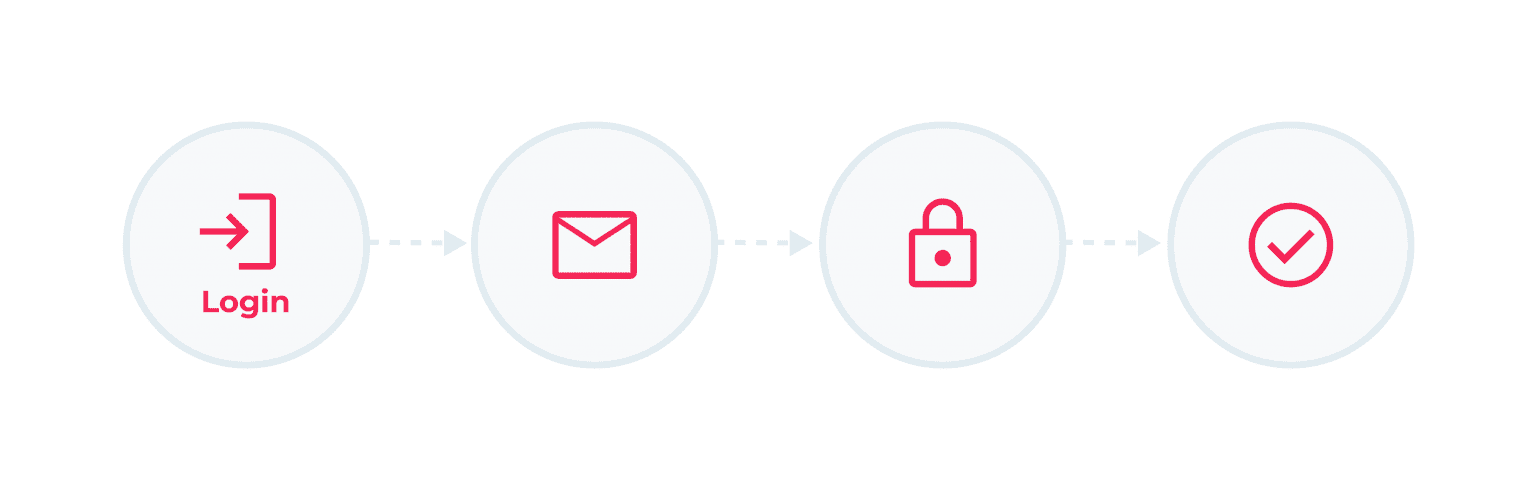
Implementing access restrictions to patients' data for employees who do not require it is an effective strategy to minimize data breaches and insider threats. By limiting access to authorized personnel, such as patients and doctors, users must authenticate themselves before accessing sensitive data. This approach provides greater control and security over the data, reducing the risk of unauthorized access.
By integrating these measures into your healthcare app development and operations, you can significantly improve data security and protect patients' sensitive information from potential breaches and cyber threats.
Data Encryption
Implementing constant data encryption in your healthcare software ensures enhanced security for data storage, connectivity, and transmission. Encryption provides protection against unauthorized access, modification, or deletion of patient records by third-party users, bolstering data security and confidentiality.
Timely Software Updates
Regularly updating your software may seem tedious, but it is crucial for maintaining robust security. Legacy software can harbor vulnerabilities that cybercriminals can exploit for data breaches or ransomware attacks. Stay vigilant and keep up with software updates provided by vendors to ensure optimal functionality and security.
Staff Training
Comprehensive employee training on digital hygiene is essential to mitigate risks posed by insider threats and user errors. Even with robust security measures in place, neglecting fundamental rules like inappropriate sharing or storage of sensitive information can jeopardize data security. Regular training sessions will promote a security-conscious culture within your organization.
Internal Security Audits
Conducting regular internal security audits is vital to assess and fortify your IT infrastructure's integrity. These audits test the internal system for malfunctions and vulnerabilities, enabling proactive identification and resolution of potential weaknesses before cybercriminals can exploit them.
Data Security Solutions for Healthcare Systems
To enhance data security in your healthcare organization, consider integrating the following solutions into your system:
Antivirus Software: Deploy robust antivirus software to detect and prevent malware, viruses, and other malicious threats from compromising your data. Regularly update the antivirus software to ensure it stays effective against the latest cyber threats.
Data Encryption Protocols: Implement data encryption protocols to safeguard sensitive patient information during storage, transmission, and connectivity. Encryption adds an extra layer of protection, making it difficult for unauthorized users to access or manipulate the data.
Back-Up and Recovery Solutions: Regularly back up your data to secure off-site locations. In the event of data loss due to cyber attacks or system failures, having reliable back-up and recovery solutions ensures you can restore critical information and minimize disruptions.
System Monitoring Software: Utilize system monitoring software to continuously monitor your IT infrastructure for any suspicious activities or anomalies. This proactive approach allows you to identify and respond to potential security breaches in real-time.
Custom Solutions: For organizations with complex IT infrastructures, cloud computing and IoT integration, or unique security requirements, considering custom-built solutions is beneficial. Tailored solutions can address specific security challenges and provide a more robust defense against targeted threats.
The size and complexity of your healthcare system will influence the scale and scope of your data security software solutions. Tailor your approach based on your organization's specific needs and risk profile to ensure comprehensive protection of sensitive data and maintain the highest level of data security in the healthcare industry.
>> Read more: Guide to Medicine Delivery App Development For Pharmacy Businesses
Conclusion
Healthcare data security is a paramount consideration when developing a secure app in the medical industry. Not only is it a mandatory requirement of federal and international data protection regulations, but data vulnerability can also lead to significant business losses and negatively impact a company's reputation and internal processes.
Fortunately, by leveraging innovative and proven technologies, you can effectively prevent data breaches and other illicit activities concerning patient PHI, while simultaneously enhancing your software and customer experience.
If you seek a professional and secure app development approach, we encourage you to contact our team at Relia Software. With real expertise in the health tech industry, we can offer cutting-edge solutions that align perfectly with your healthcare software needs and address even the most complex challenges.
>>> Follow and Contact Relia Software for more information!
- Mobile App Development
- Web application Development